When people hear that blockchains are “secure,” the explanation often sounds abstract. Decentralization, consensus, and cryptography are mentioned, but one specific tool quietly supports all of it: hashing.
Understanding cryptographic hashing in blockchain means understanding how information can be turned into digital fingerprints that help keep records reliable, tamper-resistant, and verifiable.
It’s not magic. It’s math applied in a clever way.
What a Hash Actually Is
A cryptographic hash is the result of running data through a special mathematical function. No matter how large or small the original input is, the output is a fixed-length string of characters.
This output acts like a fingerprint. Even a tiny change to the original data produces a completely different hash.
That property is what makes hashing powerful for security.
Why Hashing Is Useful
Imagine you have a document and want to ensure it hasn’t been altered. Instead of storing the entire file everywhere, you store its hash. Later, you can generate the hash again and compare.
If the hashes match, the data hasn’t changed. If they differ, something was modified.
In blockchain systems, this idea is applied constantly to verify data integrity.
How Hashing Works in Blocks
Each block in a blockchain contains data — transactions, timestamps, and other information. It also contains a hash of the previous block.
This creates a chain. If someone tries to alter an earlier block, its hash changes. That change breaks the link to the next block, which also changes its hash, and so on.
To successfully alter history, an attacker would need to recalculate hashes for many blocks and convince the network to accept them — a difficult task in well-secured systems.
The One-Way Nature of Hashing
A key feature of cryptographic hashing is that it’s one-way. You can easily generate a hash from data, but you cannot realistically reverse the process to recover the original input.
This helps protect sensitive information. Instead of exposing raw data, systems can work with hashes for verification.
In blockchain, this contributes to security without revealing everything openly.
Consistency Across the Network
Because hash functions follow strict rules, every participant in a blockchain network can independently verify results.
If two nodes run the same data through the same hashing algorithm, they get the same output. This predictability helps thousands of computers agree on what is valid.
Shared math replaces the need for centralized trust.
Hashing and Proof Systems
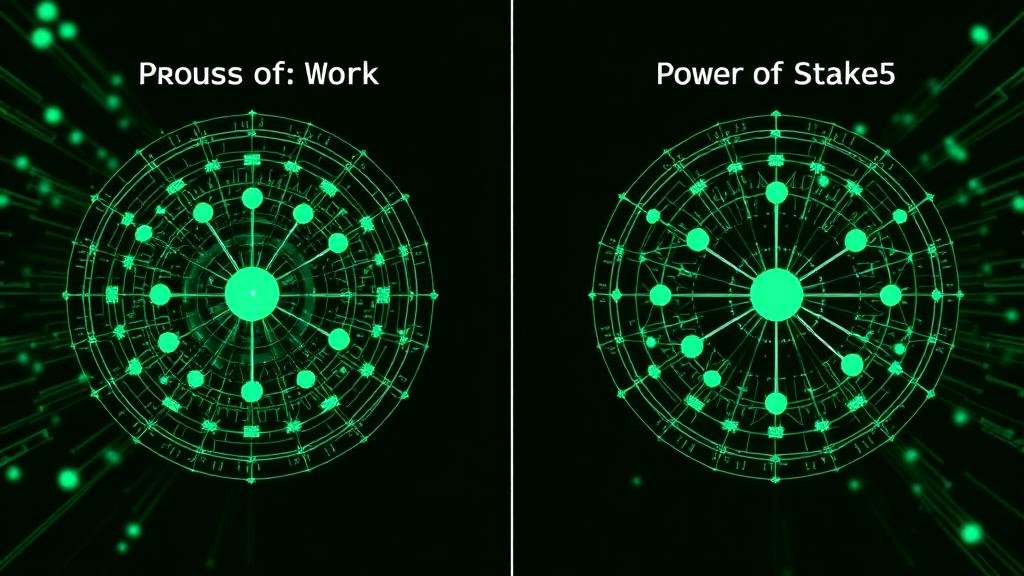
Hashing also plays a role in consensus mechanisms. In some systems, participants compete to find a hash that meets specific criteria. This process helps determine which block is added next.
The difficulty of producing certain hashes makes manipulation costly, supporting network security.
Hashing is not just about record-keeping — it’s part of how the network operates.
Why Small Changes Matter
One of the most important properties of hashing is sensitivity. Changing a single character in the input drastically changes the output.
This makes tampering easy to detect. If transaction data were altered, its hash would no longer match expectations.
This sensitivity is a cornerstone of blockchain integrity.
Human-Friendly Analogy
Think of hashing like sealing an envelope with a special wax seal. If someone opens and reseals it, the seal looks different. You know it was disturbed.
In blockchain, the “seal” is mathematical, not physical. But the principle is similar — change is visible.
Why This Matters for U.S. Readers
In the United States, digital systems are everywhere — banking, communication, identity. Trust in these systems often depends on behind-the-scenes security tools.
Understanding cryptographic hashing in blockchain helps demystify how decentralized systems can maintain reliable records without central authorities. It shows how mathematical processes replace traditional gatekeepers.
A Balanced Perspective
Hashing is powerful, but it works as part of a larger system. It doesn’t prevent all risks on its own. It supports integrity when combined with consensus rules, network design, and user practices.
Still, without hashing, blockchain security would look very different.
The Bottom Line
Cryptographic hashing turns data into unique digital fingerprints. In blockchain systems, these fingerprints link blocks together, detect tampering, and allow distributed networks to verify information independently.
It’s a quiet technology, but a foundational one — the mathematical glue that helps keep blockchain records consistent, secure, and trustworthy.