When people first buy cryptocurrency, storage is often an afterthought. The focus is on choosing a coin, watching the market, or learning how exchanges work. Security usually enters the conversation later — sometimes only after hearing about hacks or lost funds.
That’s where hardware wallets come in. Understanding hardware wallet cryptocurrency security means understanding one of the most important principles in crypto: controlling access to your assets in a way that minimizes exposure to online threats.
What a Hardware Wallet Actually Does
A hardware wallet is a physical device designed to store private keys offline. Remember, cryptocurrencies aren’t “stored” like files on a computer — they exist on a blockchain. What you control are the keys that allow you to move them.
The role of a hardware wallet is to keep those keys separated from internet-connected environments where malware, phishing attacks, and other digital threats are more common.
In simple terms, it creates a barrier between your most sensitive information and the online world.
Why “Offline” Matters So Much
Most digital attacks happen through connected systems. Computers and smartphones, while convenient, are exposed to networks, software vulnerabilities, and malicious links.
A hardware wallet reduces that exposure. When you initiate a transaction, the device signs it internally. The private key doesn’t leave the device, and the signing process is isolated from the internet.
This doesn’t make theft impossible, but it significantly reduces the risk from common online attack methods.
Not Just for Experts
Some people assume hardware wallets are only for advanced users or large investors. In reality, they are tools designed to make secure self-custody more manageable.
The goal isn’t to complicate things. It’s to make good security practices easier to maintain by default. Instead of relying on a general-purpose device like a laptop, users rely on a device built specifically for key protection.
Security improves when tools match the task.
What They Protect Against
Hardware wallets are particularly effective against:
Malware that scans devices for keys
Keyloggers that record input
Remote attackers trying to access files
Phishing sites attempting to capture sensitive data
Because private keys never directly touch an internet-connected environment, many common attack paths are blocked.
However, this protection only works when users understand the basics of how to use the device correctly.
The Human Factor Still Matters
Even the most secure device cannot protect against every mistake. Social engineering, phishing, and careless handling of recovery phrases remain risks.
Hardware wallets protect keys, but users must still:
Verify transaction details on the device screen
Keep recovery phrases stored securely
Avoid sharing sensitive information
Be cautious with software and links
Security is always a combination of tools and habits.
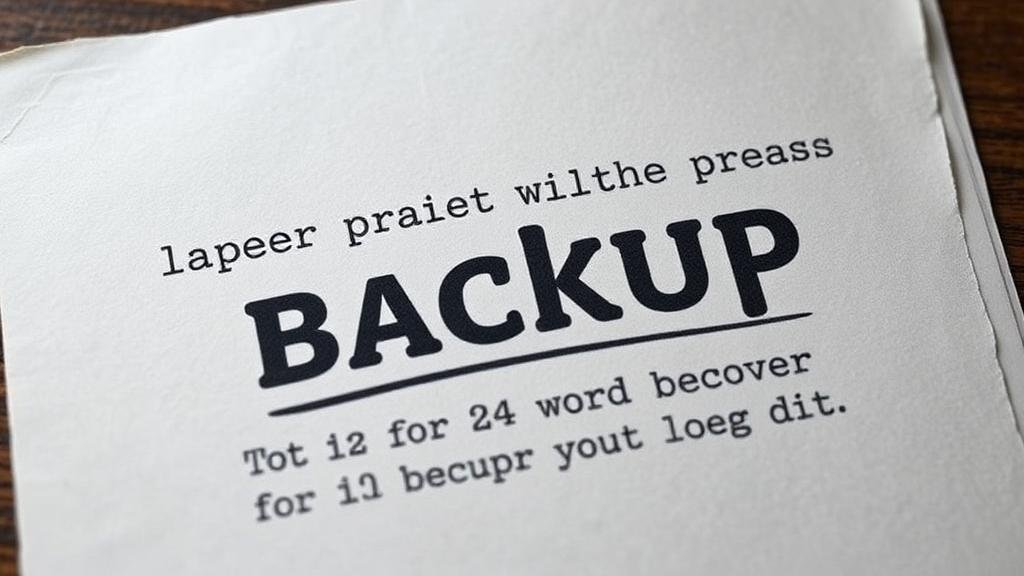
Recovery Phrases: The Real Backup
When setting up a hardware wallet, users receive a recovery phrase — a series of words that can restore access if the device is lost or damaged.
This phrase is critical. Whoever has it can control the assets. It must be stored offline, safely, and never entered into websites or shared.
In many ways, the recovery phrase is more important than the device itself.
Convenience vs. Security
Hardware wallets add a small layer of friction. Transactions require physical confirmation, and access is not as instant as clicking a button on an app.
That trade-off is intentional. Slowing down sensitive actions reduces the chance of impulsive or accidental mistakes. It introduces a pause that improves decision-making.
Security often benefits from thoughtful inconvenience.
Why This Matters for U.S. Users
In the United States, many people are used to financial systems that offer account recovery, fraud reversal, and institutional support. Crypto’s self-custody model works differently.
Hardware wallets help bridge that gap by providing a structured, secure way to hold assets independently. They don’t replicate bank protections, but they offer a strong method for reducing technical risk.
A Balanced View
Calling hardware wallets the “gold standard” doesn’t mean they are perfect. They can be lost, damaged, or misused. They don’t eliminate the need for awareness.
But when it comes to hardware wallet cryptocurrency security, they represent one of the most effective ways to protect private keys from online threats — which are among the most common risks in crypto.
The Bottom Line
Crypto ownership ultimately comes down to key control. Hardware wallets provide a dedicated, offline environment designed specifically for that purpose.
They don’t replace good habits. They support them.
In a system where personal responsibility plays a central role, using tools built for security is one of the most practical steps users can take to protect their digital assets.